When I first heard of Laudanum, I really wasn’t quite sure what it did, or what it was. I was thinking it was an actual application. I first avoided it a little just because I wasn’t quite sure how I could use it or how it really worked. If you are in the same situation, then hopefully this introduction will help shed some light on what it is and how it can be used.
So What is Laudanum?
Laudanum is not an application, but rather a repository of inject-able files. On its own, it doesn’t do anything. These files can be deployed to a target machine and then executed to perform specific functionality. More information about the team that works on Laudanum can be found on the Laudanum: Injectable Functionality site.
What are the Files?
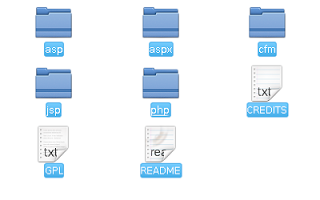
The files are really just scripts written in different languages to provide as much coverage as possible. Laudanum targets web servers so the scripts are written for Cold Fusion, Classic ASP, ASP.Net, Java, and PHP. The image below shows the languages covered in the current version of Laudanum:
What Can it Do?
Laudanum consists of a few features that can be really big during a security assessment. These features may be limited depending on the environment you are deploying to. For example, the JSP files may contain different functionality than the ASPX files. The common goal is to provide shell access, file browsing capabilities, DNS queries, LDAP retrieval and others. The image below shows some of the files for the PHP options:
In addition to these features, most of the files also include the ability to limit access to the file to specific IP addresses. You might question why that is necessary. Imaging for a moment you are testing a client’s system and you deploy one of these files to the server. If this was not just limited to you, the tester, then if someone else found this file they could use it for evil. We want to protect the client as much as we can and being able to limit access to these files is critical. This does mean that you have to configure the file before you deploy it.
I will be diving deeper into the functionality of some of these files in my next few posts.
How is it Deployed?
There are multiple ways to deploy the Laudanum files. For example, a SQL Injection vulnerability may be used to deploy the file to the server. Server management features can be used. I have used TomCat’s deployment capabilities numerous times to deploy these files to a server. File upload functionality in web pages may also be used. There are many ways that a file could be deployed, and of course, it all depends on the set up of the server as to what may or may not work.
Where Can I Get It?
Laudanum is open source and available at http://sourceforge.net/projects/laudanum/. It is also included in the SamuraiWTF distribution platform, which also contains many other great tools for penetration testing.
Wrap Up
This was just a brief intro to what the Laudanum project is and how it is used. The key thing to remember is that it is not an application, but just a collection of files that can be deployed to a server through an already existing vulnerability. Although this doesn’t seem like all that much, these files have been the gateway into a lot of servers during assessments. Don’t underestimate the power of these scripts as they can be critical during an assessment given the right circumstances. I will dig deeper into the ways that this can be used in my next few posts.
James Jardine is a Principal Security Consultant with Secure Ideas.
If you are in need of a penetration test or other security consulting services you can contact him at james@secureideas.com or visit the Secure Ideas – Professionally Evil site for services provided.