First you should have sqlmap downloaded and installed on your machine used for testing. If you don’t want to install it, Samurai WTF and Kali Linux comes with this pre loaded.
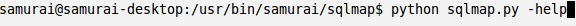
To launch sqlmap in Samurai we will just open up a shell, browse to the /usr/bin/samurai/sqlmap directory, and type in python sqlmap.py. However, sqlmap requires parameters to run. We can issue the -help command to get help on the tool. Below is a screenshot of the command:
- Target
- Request
- Injection
- Enumeration
The target parameter is a requirement as it specifies which URL for sqlmap to test against. An example of this would be:
The next parameter category is the request parameter. Below are some useful request parameters with descriptions:
- Data – The ability to put a data string in a request to make it a POST request
- Cookie- Set a cookie for the request
- Random-Agent – Randomizes user-agent header value
- Force-ssl – Very useful on sites that are SSL based
- Proxy – Great for troubleshooting. Instructs sqlmap to use a proxy (Burp works great)
The next parameter category is the injection parameter. This parameter allows you to specify the back end DBMS if you know it, and to specify a parameter. By default, if no parameter is specified, sqlmap will try all parameters. We will build on the above example and specify a mysql backend.
Finally, the last parameter category field we are going to talk about is enumeration. Enumeration gives you the ability to grab banners, current users, current database, passwords, tables, columns, schema’s and even allows the full database dump. Using the example above we can enumerate and dump the entire database using the following command:
To learn more about sqlmap you can use the help page or find more information online here. If your looking for something to test against in a sandboxed environment you could try Mutillidae.
Professionally Evil Toolkit (PET) is a blog series about tools that security professionals use in the industry. These tools can be used for many things including penetration testing, auditing, and testing. The tools mentioned in PET can be very dangerous when ran on production systems. Secure Ideas recommends you get authorization from the appropriate system owners and test against staging environments prior to running these tools.
Jeff Bleich is a Senior Security Consultant with Secure Ideas. If you are in need of a penetration test or other security consulting services you can contact him at jeff@secureideas.com or visit the Secure Ideas – Professionally Evil site for services provided.